As the adoption of Amazon Web Services (AWS) continues to rise, ensuring the security of your AWS environment is of utmost importance. In this blog post, we will explore the significance of detective controls in AWS security and how they act as a powerful mechanism for identifying and responding to security incidents. Join us as we dive into the world of AWS detective controls and discover effective strategies for bolstering your platform’s security.
Cloud Security on Amazon Web Services (Part II)
Bolstering AWS Security: Harnessing the Power of Detective Controls
Strengthening AWS Security: The Role of Detective Controls
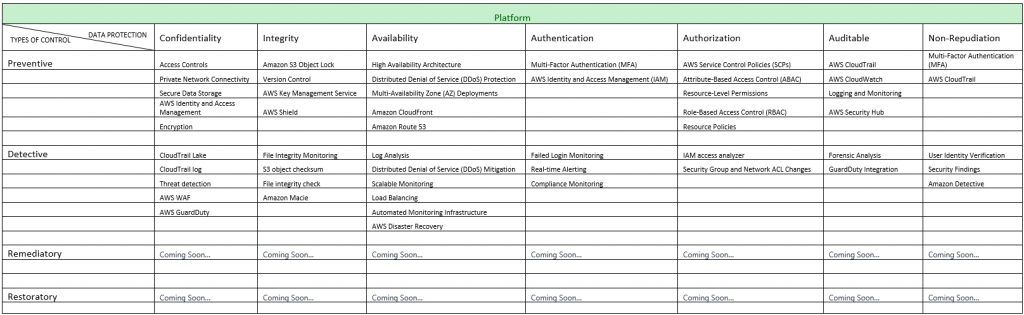
Detective | Confidentiality
-
- AWS CloudTrail lake: Combined with Key Management Service (KMS), strengthens platform layer detective security by ensuring encrypted storage of API activity logs, protecting sensitive data, and enabling secure access control and key management.
- AWS CloudTrail logs: Empower platform layer detective security by capturing and providing detailed insights into API activity, enabling threat detection, anomaly analysis, and configuration monitoring within AWS environments.
- Threat detection: Analyzing (CloudTrail logs) helps detect security threats and anomalies in API activity.
- AWS WAF: AWS WAF logs detailed information about web requests, including headers, payloads, and request attributes. These logs provide valuable insights into potential security incidents, enabling proactive detection, investigation, and response to suspicious activities or attacks.
- AWS GuardDuty: Enhances platform layer detective security by continuously monitoring and analyzing AWS account activity, network traffic, and AWS service configurations to detect and alert on potential security threats, vulnerabilities, and unauthorized access attempts.
Detective | Integrity
-
- File Integrity Monitoring (FIM): Utilize FIM tools to monitor critical system files, configurations, and directories for any unauthorized changes or tampering.
- S3 object checksum: Is a mechanism used to ensure the integrity of objects stored in Amazon S3 (Simple Storage Service). The checksum is a value computed from the object’s data, and it is used to verify that the object hasn’t been corrupted or tampered with during storage or transmission.
- File integrity checks: File integrity checks can be performed using various mechanisms and services provided by AWS. One such service is AWS Config, which enables continuous monitoring and assessment of resource configurations and compliance rules.
- Amazon Macie: Amazon Macie is a data security service that discovers sensitive data by using machine learning and pattern matching, provides visibility into data security risks, and enables automated protection against those risks.
Detective | Availability
-
- Log Analysis: Analyze system logs and event data using tools like AWS CloudWatch Logs or third-party SIEM solutions to identify potential availability issues, such as service disruptions or resource exhaustion.
- Distributed Denial of Service (DDoS) Mitigation: Implement DDoS detection and mitigation services to identify and respond to DDoS attacks that may impact availability.
- Scalable Monitoring: Autoscaling groups can be integrated with monitoring services like Amazon CloudWatch, enabling the collection of metrics and logs from instances. This allows for comprehensive monitoring of system activity and behavior, aiding in the detection of integrity-related issues or suspicious activities.
- Load Balancing: By leveraging load balancing at the detective level in the platform layer, organizations can enhance security monitoring capabilities through distributed traffic analysis, resilience, scalability, fault detection, SSL/TLS termination, and centralized logging.
- Automated Monitoring Infrastructure: High availability architectures often incorporate automated monitoring infrastructure provisioning and configuration management. This automation helps streamline the deployment and management of monitoring components, reducing the risk of configuration errors and improving overall system reliability.
- AWS Disaster Recovery: AWS offers services like AWS Backup, AWS CloudEndure, and AWS Site Recovery that enable organizations to implement robust DR solutions. These services help replicate and restore data, applications, and infrastructure in case of a disaster, ensuring business continuity.
Detective | Authentication
-
- Failed Login Monitoring: Monitor and log failed login attempts to identify potential brute-force attacks or unauthorized access attempts.
- Real-time Alerting: When a CloudWatch Events rule is triggered, it can send an alert using SNS. SNS allows you to send notifications to various destinations. By configuring SNS to receive CloudWatch Events alerts, you can be notified in real-time about potential security incidents, allowing for immediate investigation and response.
- Compliance Monitoring: VPC Flow Logs provide an audit trail of network traffic, helping organizations demonstrate compliance with regulatory requirements and industry standards. The logs can be reviewed to ensure adherence to network security policies, access controls, and data protection measures.
Detective | Authorization
-
- AWS CloudTrail: AWS CloudTrail provides detailed logs of API calls and activities within your AWS account. It records important events such as user logins, API calls, resource modifications, and security-related events. CloudTrail logs are stored in Amazon S3 and can be used for security analysis, troubleshooting, and compliance purposes. CloudTrail also integrates with AWS CloudWatch for real-time monitoring and alerting based on specific events.
- AWS CloudWatch: AWS CloudWatch is a monitoring and logging service that collects and tracks metrics, logs, and events across your AWS resources and applications. CloudWatch provides a centralized dashboard for monitoring performance, generating alarms, and triggering notifications based on predefined thresholds. It allows you to gain visibility into your environment and facilitates auditing by capturing and analyzing logs and metrics.
- Logging and Monitoring: Enable AWS CloudTrail to log API calls and AWS Config to track configuration changes and utilize AWS CloudWatch for monitoring and alerting on specific events or metrics.
- AWS Security Hub: AWS Security Hub is a comprehensive security service that provides a centralized view of security findings and compliance status across multiple AWS accounts. It aggregates and prioritizes security alerts from various AWS services, third-party security tools, and AWS partner solutions. Security Hub helps you identify security risks, manage compliance, and track the resolution of security findings.
Detective | Auditable
-
- Forensic Analysis: CloudTrail logs in the lake enable forensic analysis for security incidents, aiding in event reconstruction and root cause investigation. They serve as valuable evidence, helping identify involved parties and analyze post-incident sequences.
- GuardDuty Integration: GuardDuty can be configured to use the CloudTrail logs stored in the log bucket as a data source for threat detection. GuardDuty automatically analyzes the logs and applies machine-learning algorithms to identify potential security threats and anomalies.
Detective | Non-Repudiation
-
- User Identity Verification: MFA adds an additional layer of verification to confirm the user’s identity during critical operations or high-risk activities. This ensures that the actions are performed by authorized individuals and reduces the risk of unauthorized activities.
- Security Findings: GuardDuty generates detailed security findings from log analysis, providing evidence of incidents and supporting non-repudiation by linking activities to their impact.
- Amazon Detective: Amazon Detective accelerates analysis, investigation, and root cause identification of security findings and suspicious activities. It automatically collects log data from AWS resources and offers prebuilt data aggregations, summaries, and context for swift analysis and understanding of security issues.
Written By: Umashankar N, Matheshsivatharshan S, and Preeth M
If you have any questions or suggestions, please reach out to us at contactus@1cloudhub.com
Tags:
