In today’s fast-paced world where speed, consistency, and accuracy are paramount, DevOps has revolutionized the way organizations design, develop, and maintain their IT infrastructure. Automation of infrastructure has replaced the tedious, manual process of managing IT infrastructure. It also helps to avoid errors and is helping engineers automatically launch cloud environments quickly and without mistakes.
In this three-part blog series, we will walk you through the options we use to automate IaC and how you can use them as well.
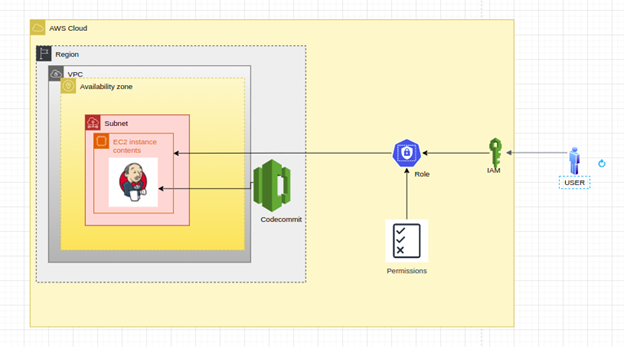
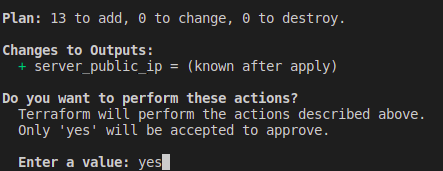
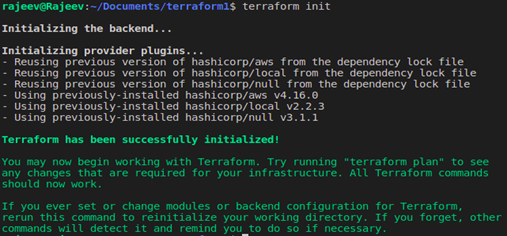
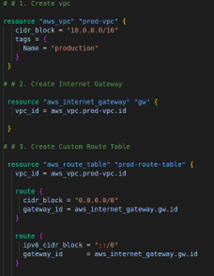
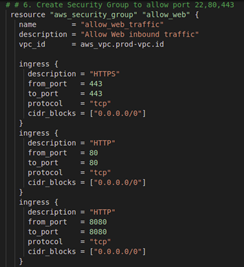
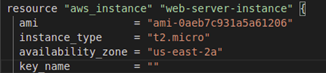
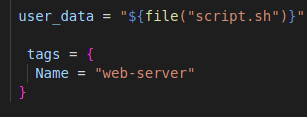
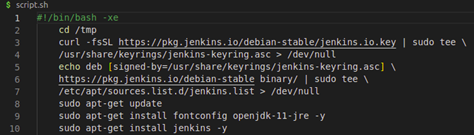
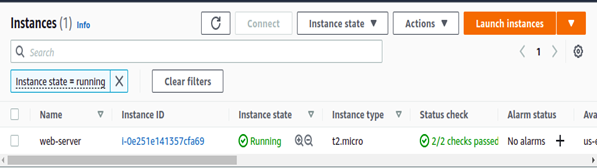
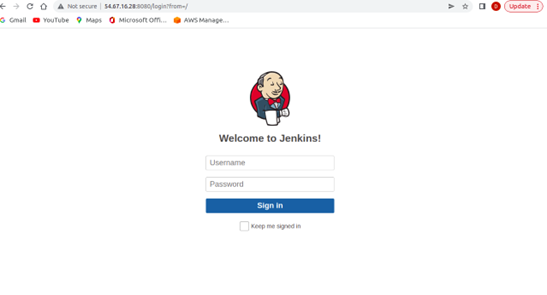
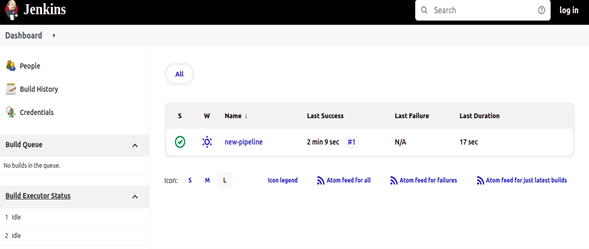
In this first blog of the series, we will learn about Terraform and its use with userdata. The concept is to build infrastructure by automating it with Terraform as Iac(Infrastructure as a code). We’ll use this to install Jenkins and its plugin, as well as run a simple pipeline script by automation. Terraform is our go-to tool for managing the whole infrastructure lifecycle with infrastructure as code.
Infrastructure As Code
Iac is all about managing and provisioning infrastructure through code instead of through manual processes. The purpose of Iac is to simplify the process of large-scale management of infrastructure. Iac basically means managing your IT infrastructure using configuration files.